Good Morning, Buffalo: Billions of gallons of sewage still flow into Buffalo's rivers. Can the sewer authority keep up?

Biden condemns racist theory of white supremacy in visit to Buffalo after mass shooting - Source New Mexico

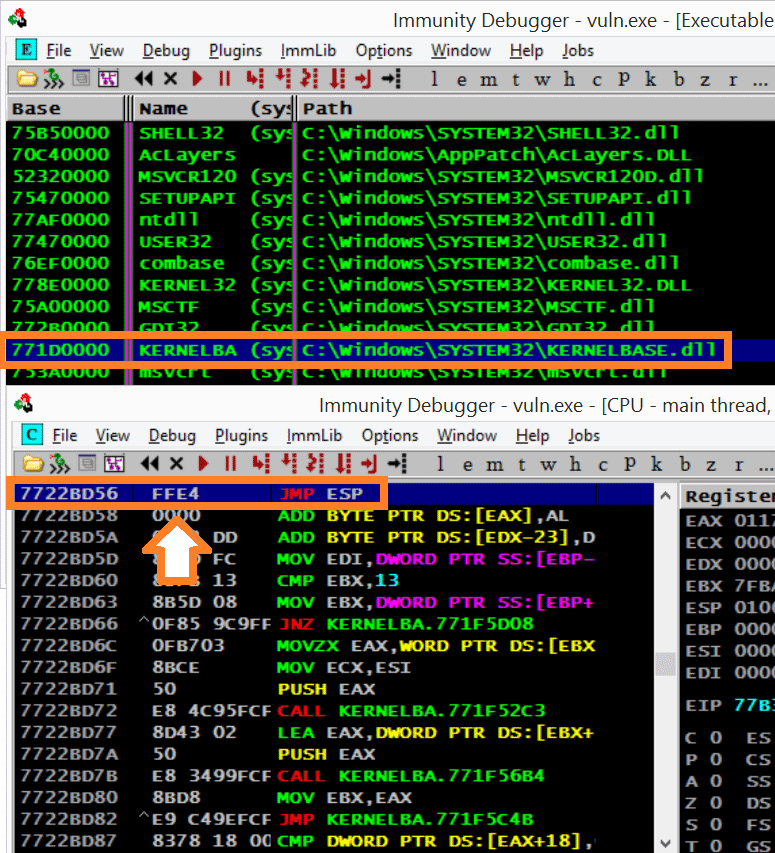
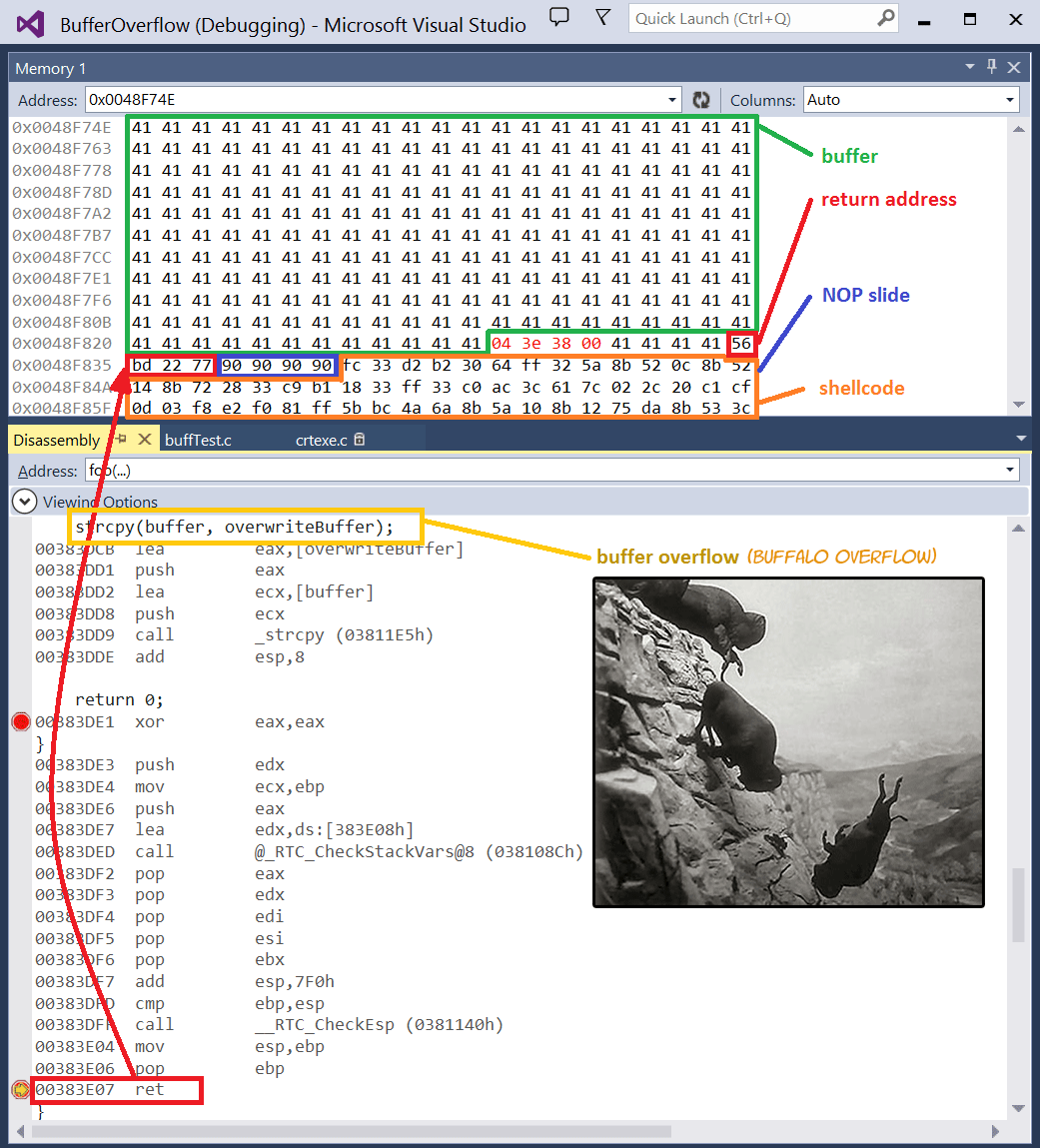
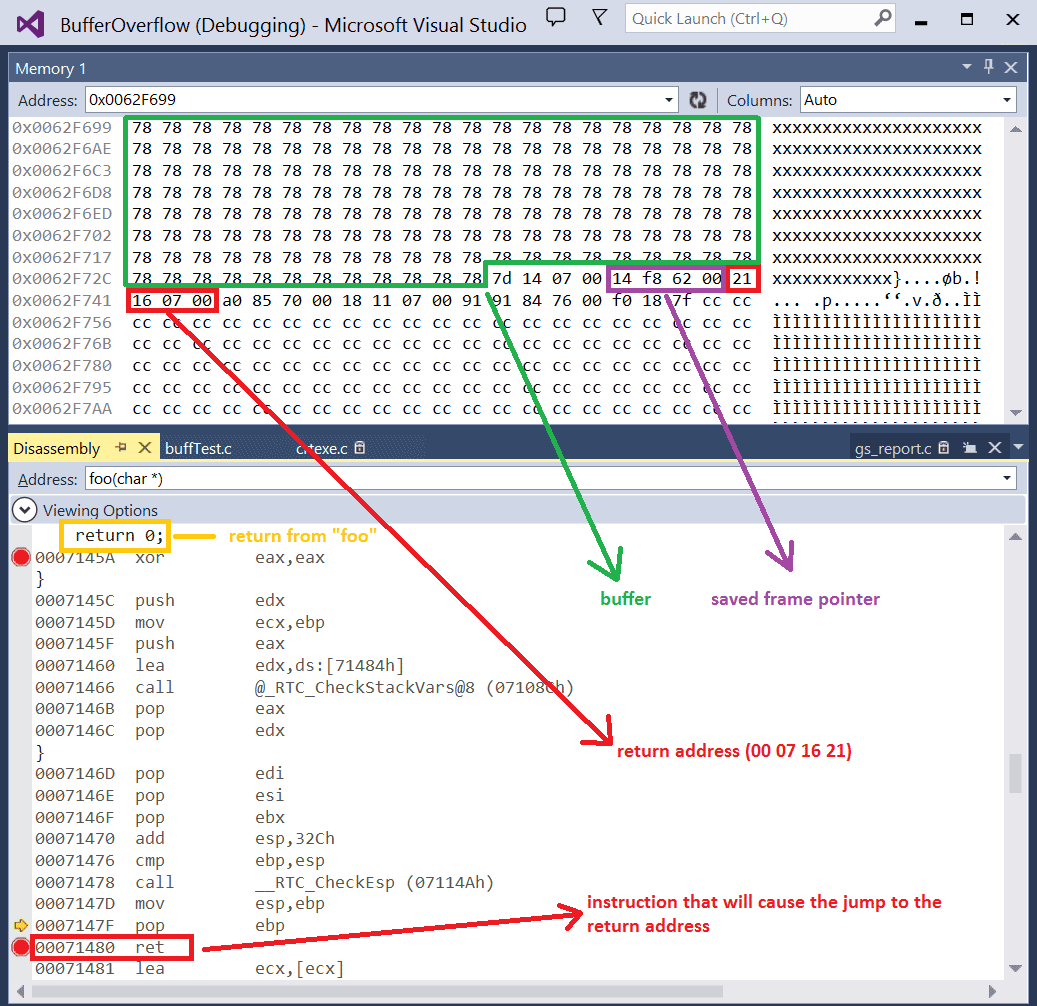
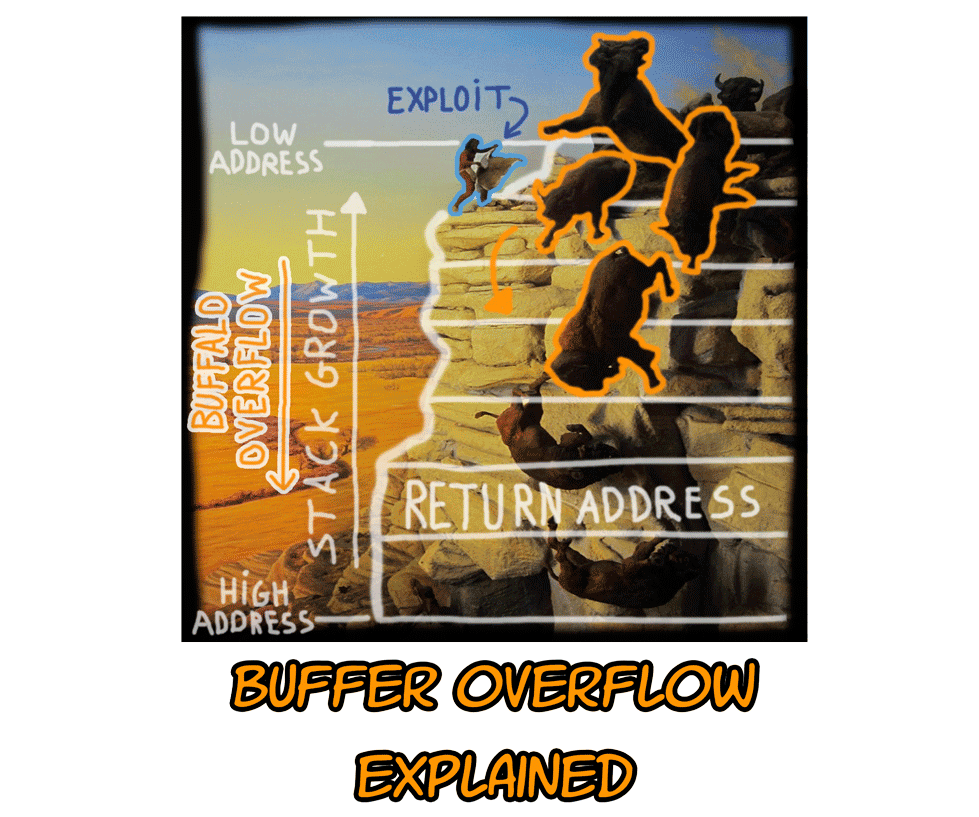
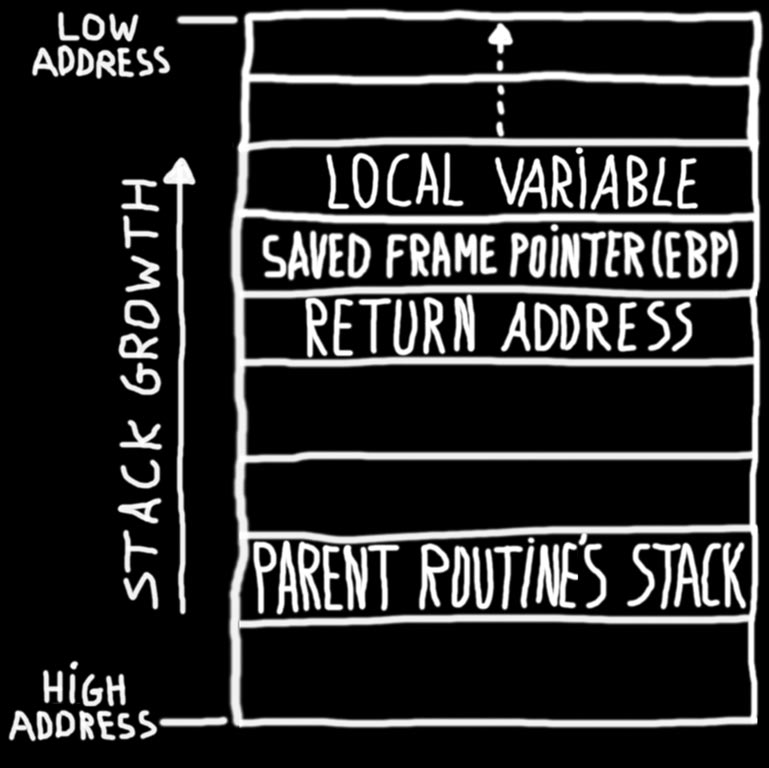
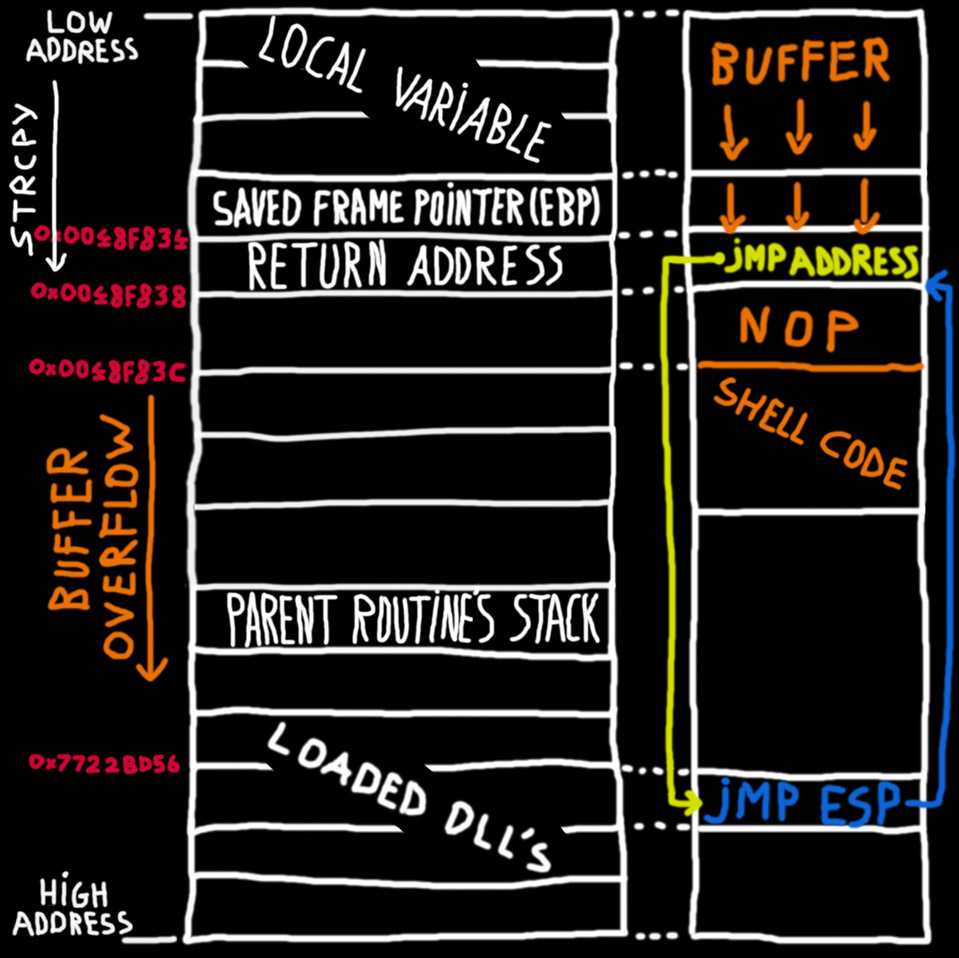
Buffer Overflow.pdf - SEED Labs Buffer Overflow Vulnerability Lab 1 Buffer Overflow Vulnerability Lab CS 4264 PROJECT 1 Spring 2017 c 2006 - 2014 | Course Hero

Buffer Overflow Lab.docx - Buffer Overflow Lab Based heavily on a lab developed by Wenliang Du of Syracuse University as part of the SEED labs series | Course Hero

Buffalo transplants, voting rights among the losses this session recalled by Native lawmakers – Daily Montanan

Buffer Overflow Lab.docx - Buffer Overflow Lab Based heavily on a lab developed by Wenliang Du of Syracuse University as part of the SEED labs series | Course Hero