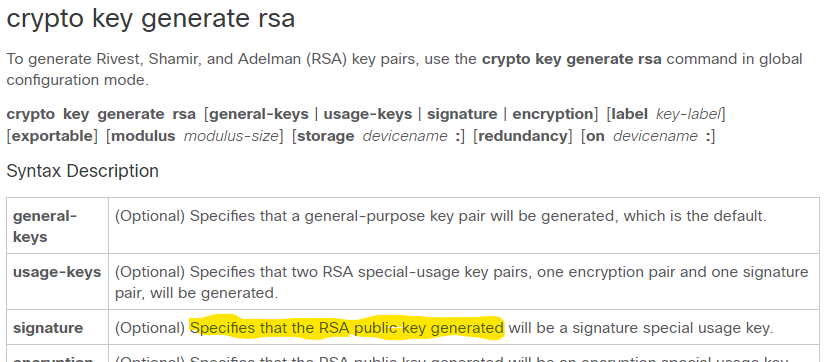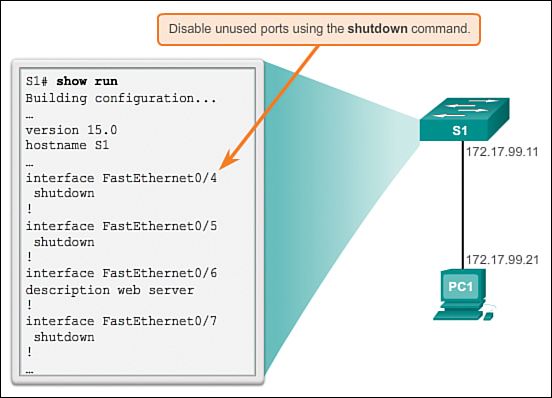
Switch Security: Management and Implementation (2.2) > Cisco Networking Academy's Introduction to Basic Switching Concepts and Configuration | Cisco Press

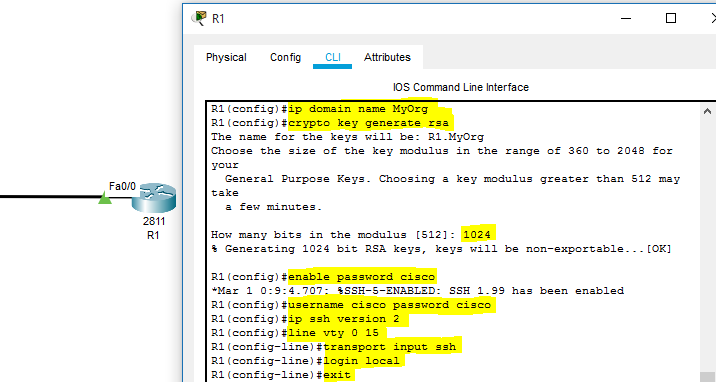
9 Steps Setting Up Cisco Router | ITPro Today: IT News, How-Tos, Trends, Case Studies, Career Tips, More

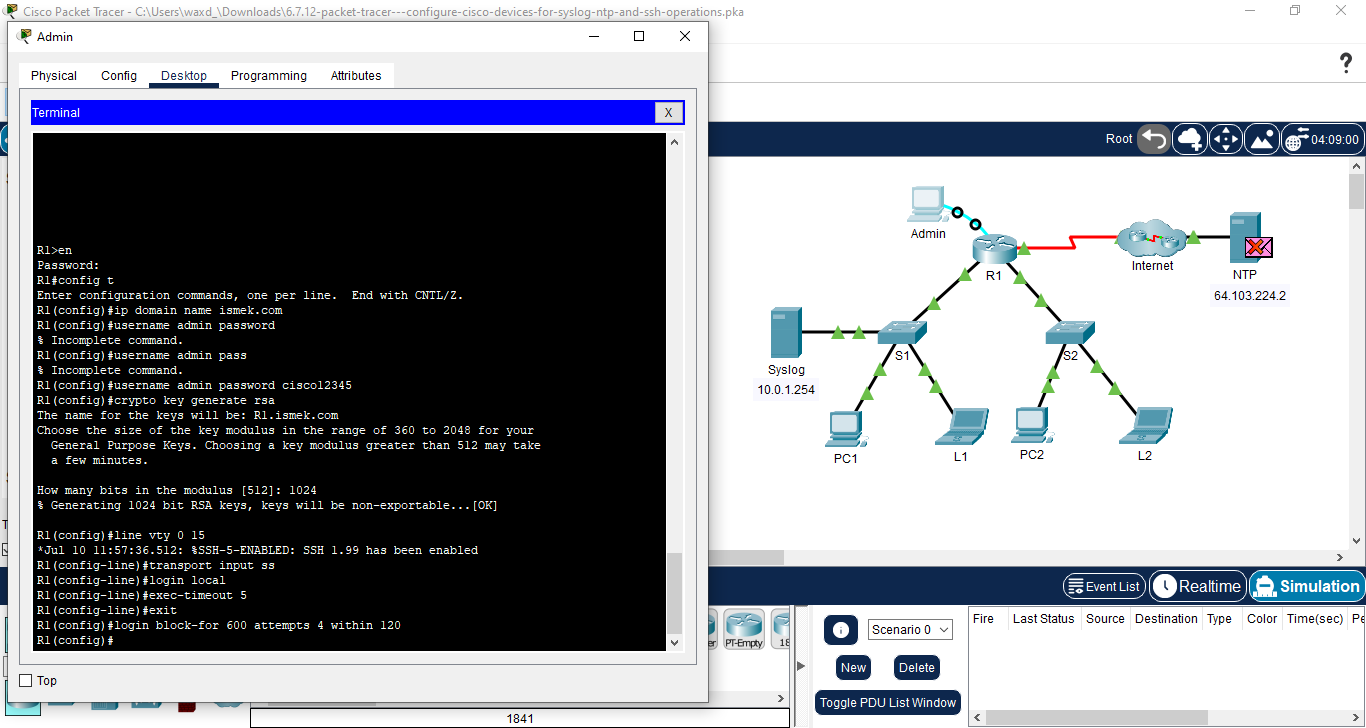
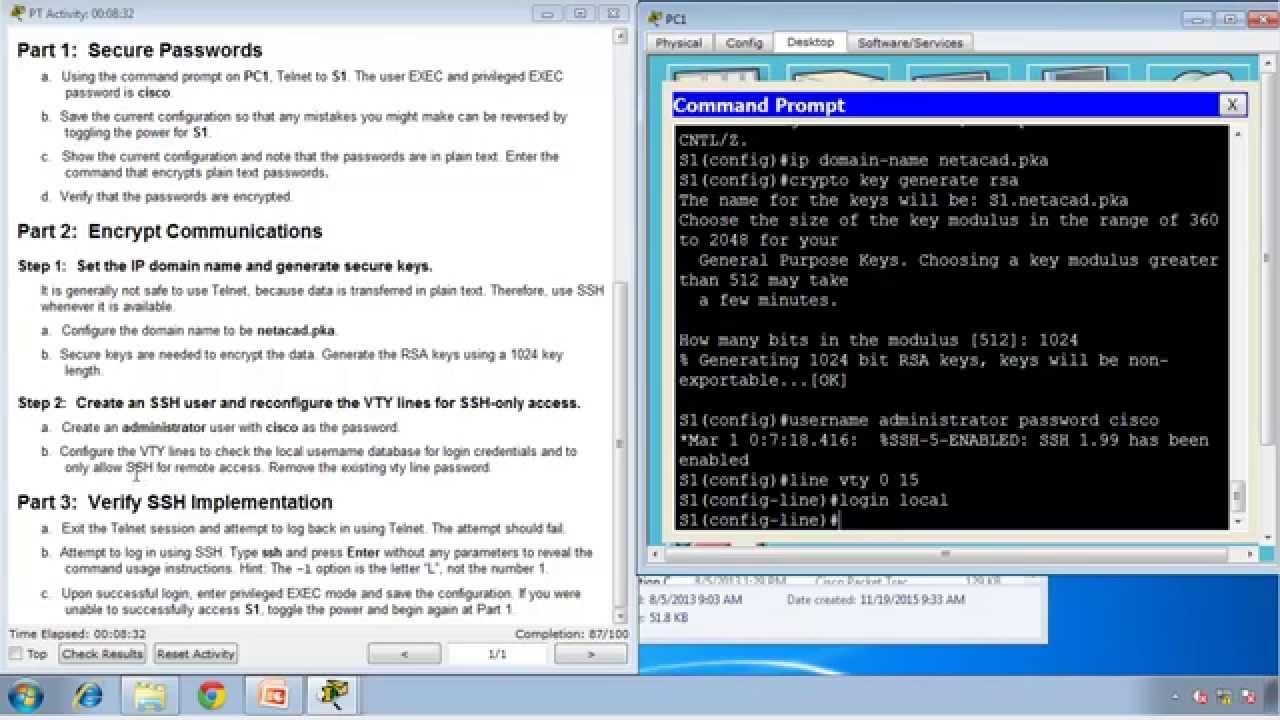
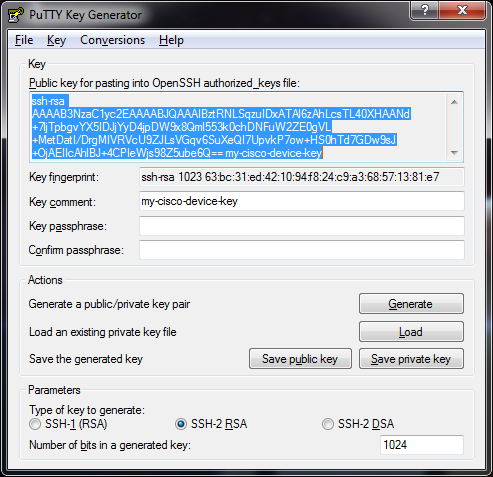
Configure Cisco Router Step by Step Guide - Learn how to secure (Enable & Privilege Exec Mode), - Studocu