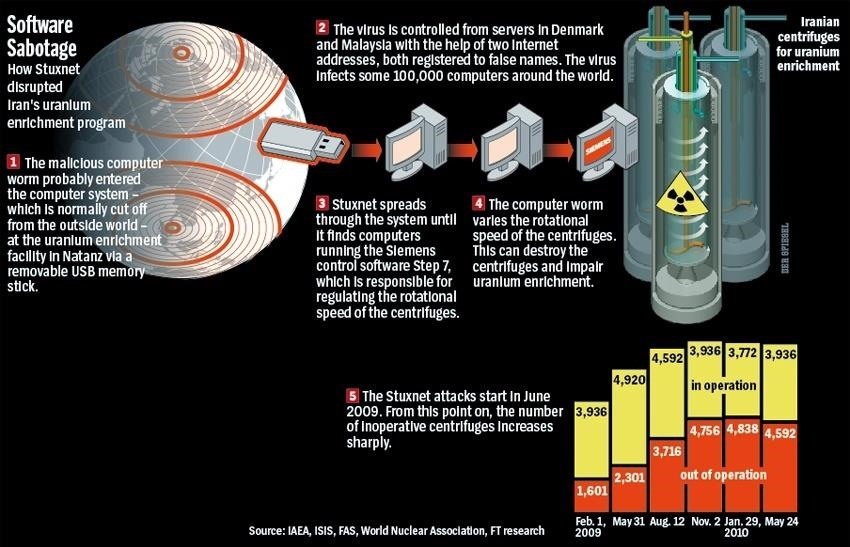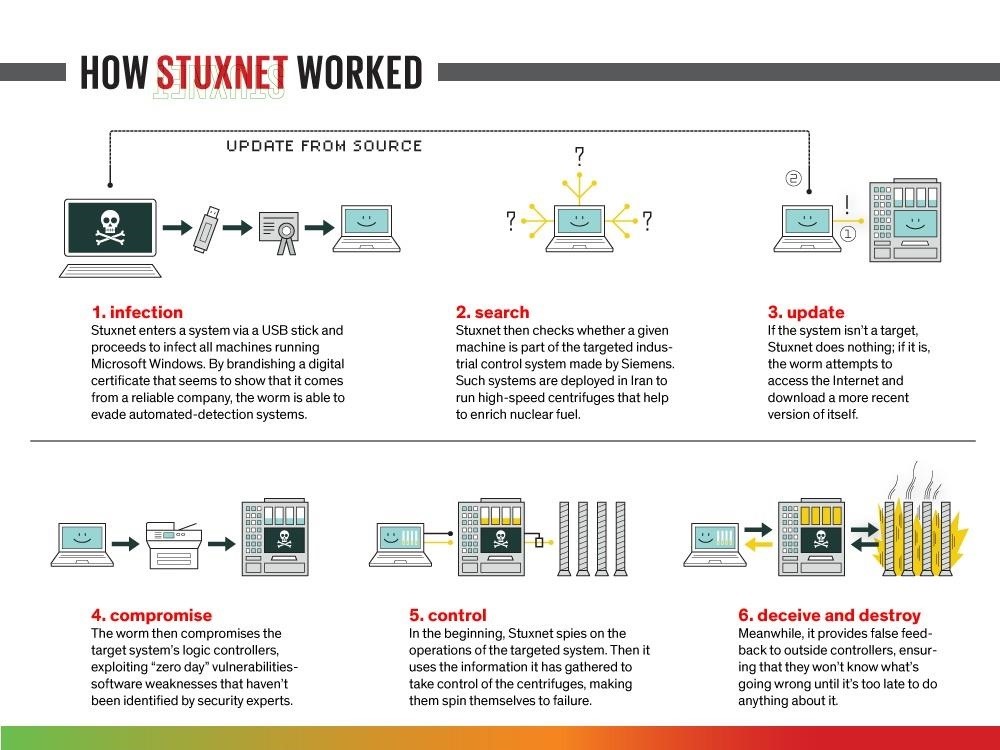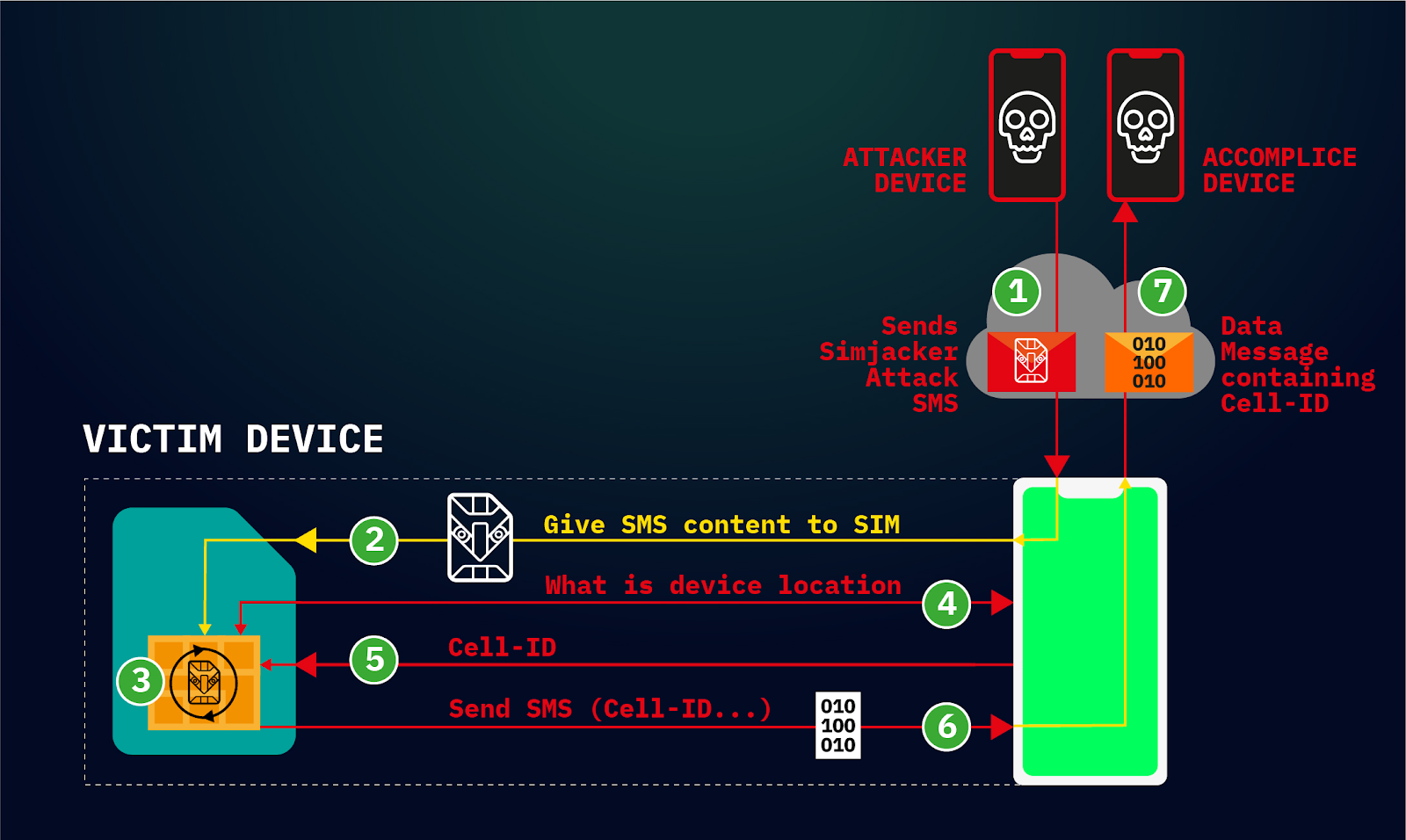
A new Stuxnet-level vulnerability named Simjacker used to secretly spy over mobile phones in multiple countries for over 2 years: Adaptive Mobile Security reports - Security Boulevard
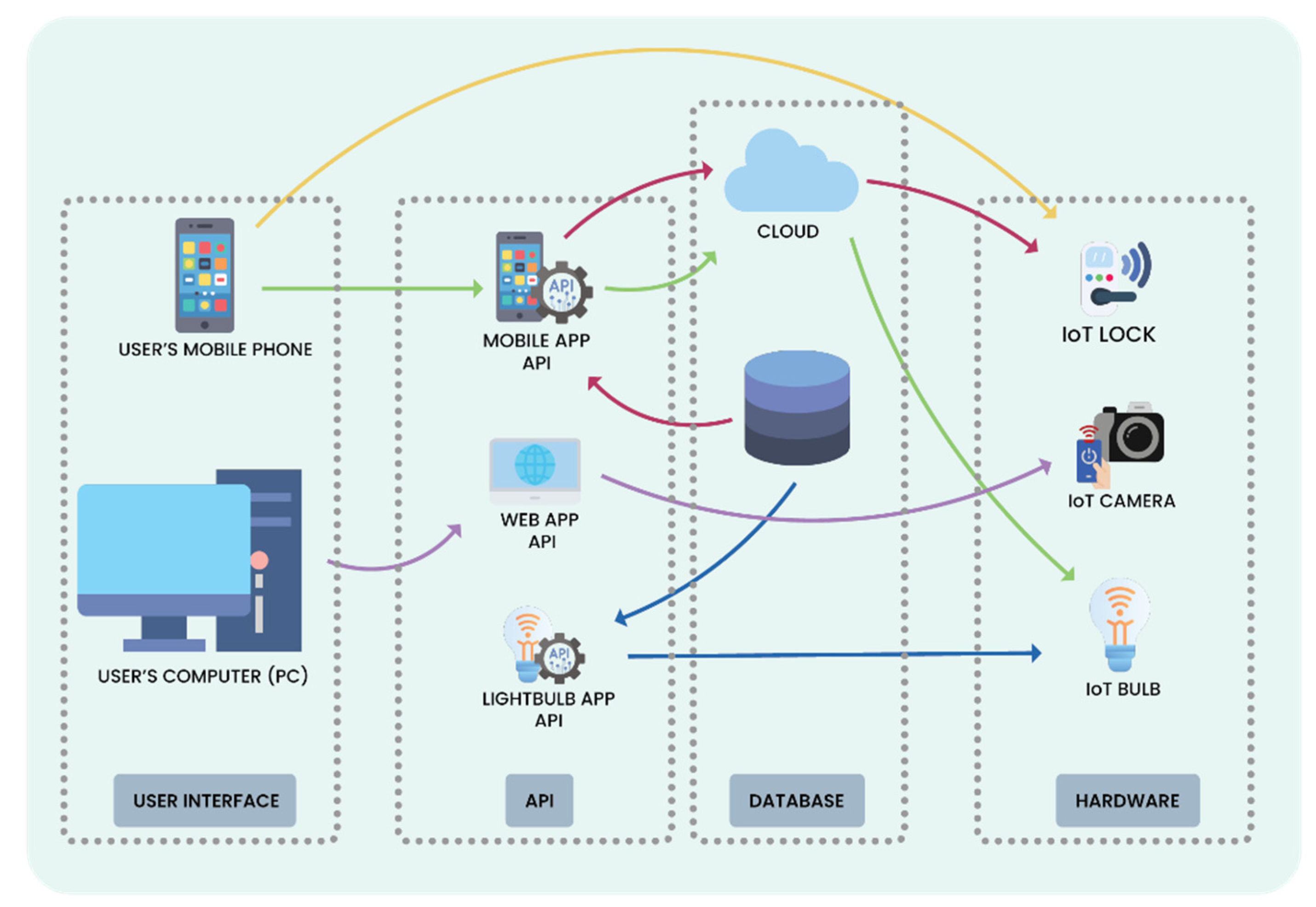
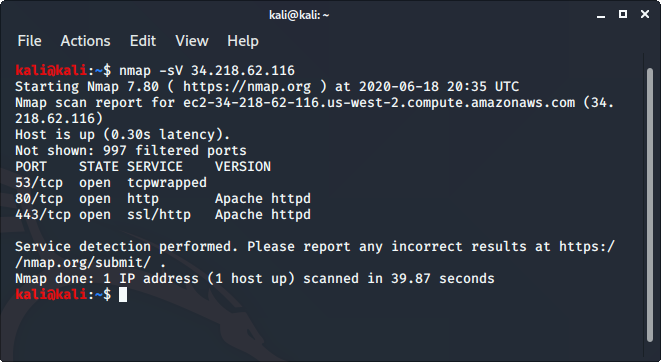
Future Internet | Free Full-Text | Automated Penetration Testing Framework for Smart-Home-Based IoT Devices