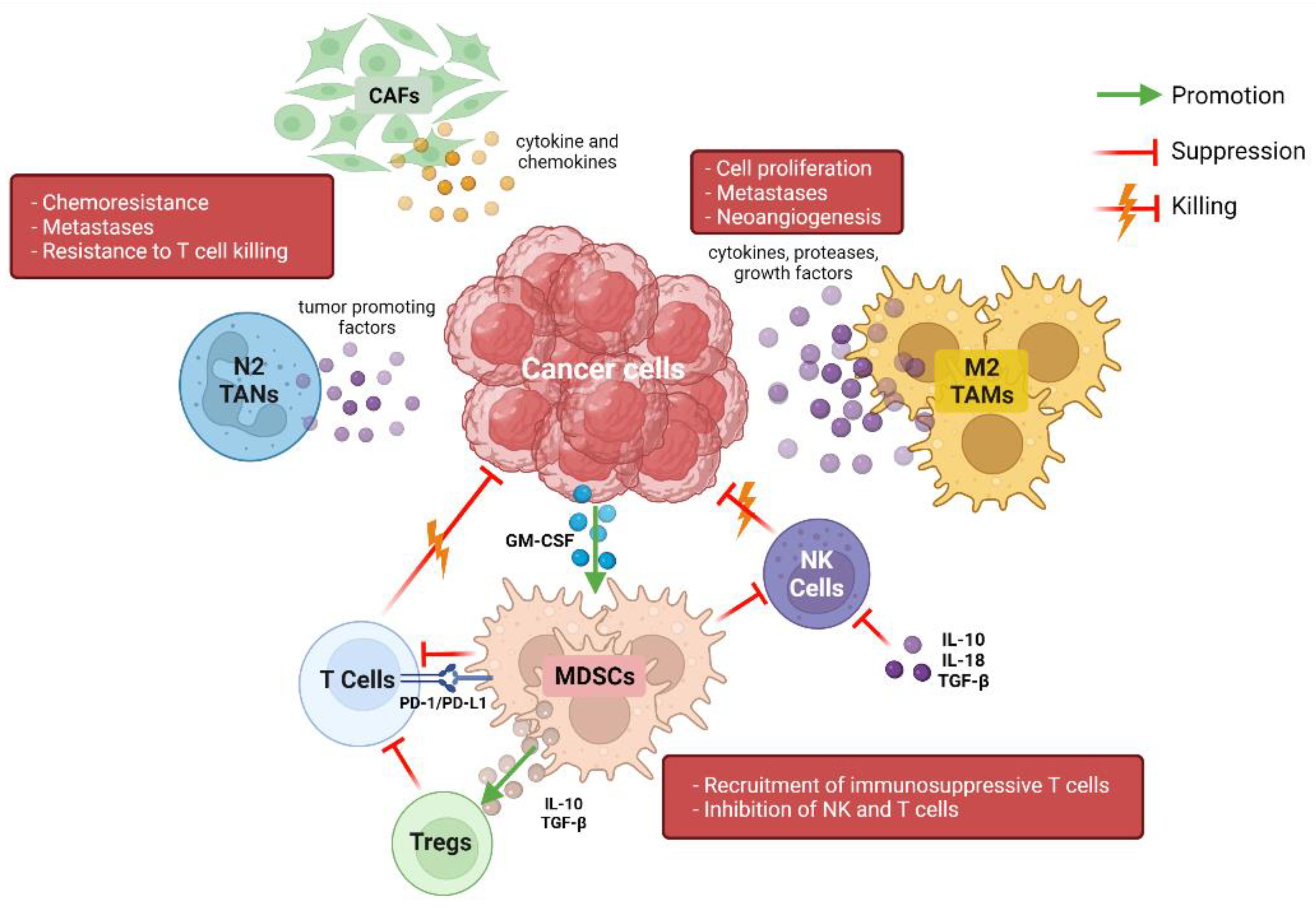
Cancers | Free Full-Text | Immunotherapy in Pancreatic Cancer: Why Do We Keep Failing? A Focus on Tumor Immune Microenvironment, Predictive Biomarkers and Treatment Outcomes

Wave power generation for 2004 For year 2004 it show that the highest... | Download Scientific Diagram

Capturing Chemistry in Action with Electrons: Realization of Atomically Resolved Reaction Dynamics | Chemical Reviews

Identities and Foreign Policies in Russia, Ukraine and Belarus | PDF | Post Soviet States | European Union

Processing of Materials for Regenerative Medicine Using Supercritical Fluid Technology | Bioconjugate Chemistry
PDF) A Review of the Biology of Cerataphidini (Hemiptera, Aphididae, Hormaphidinae), Focusing Mainly on Their Life Cycles, Gall Formation, and Soldiers
PDF) Invasive Optical Pumping for Room-temperature Masers, Time-resolved EPR, Triplet-DNP, and Quantum Engines exploiting Strong Coupling